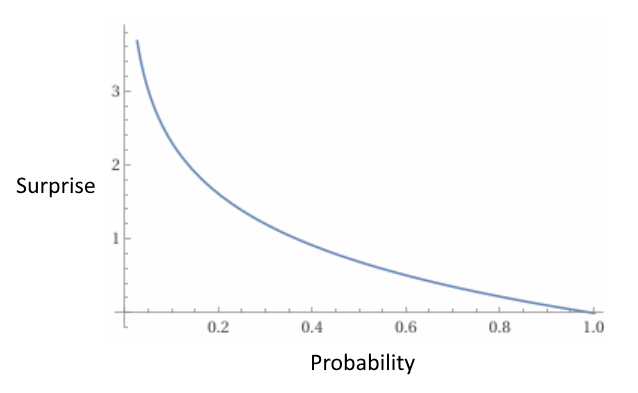
Surprise has the extremely special distinction of being both an emotion and a completely quantifiable thing that scientists and mathematicians talk about very frequently. Whenever probability is a thing, surprise is also a thing. It’s true and it’s not even that complicated! Watch:
For some intuition:
You’re certain the sun will rise tomorrow; you believe the probability the sun will rise is 100% or “1”; we have that -log(1) = 0. So if the sun rises tomorrow, your level of surprise will be 0. That sounds correct!
If someone flips a coin, you believe the probability it’ll land heads is 50% aka 0.5. We have that -log(0.5) = 0.3; your level of surprise at it landing on heads is 0.3
If they flip the coin again, and get heads again, your level of surprise is 0.3 + 0.3 = 0.6 surprise. Yes, this actually works, you can just add them, no need to fuss around with subtracting from 1 then multiplying
To turn that first one around, you believe the probability the sun won’t rise tomorrow is 0% or “0”. We have that -log(0) = ∞. If the sun doesn’t rise tomorrow, your level of surprise will be ∞. Personally, this is pretty intuitive to me!
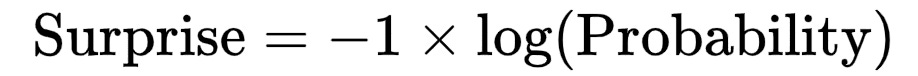
Hell is other people’s understanding of statistics
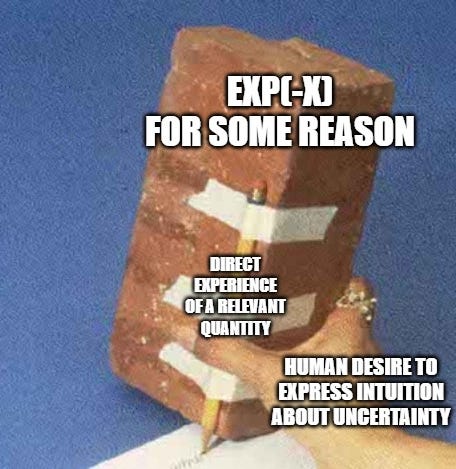
People talk about uncertainty in an intuitive way constantly. They use words like “might”, “maybe”, “could do”, “there’s a distinct possibility”. So weaselly! I often wish people would be more quantitative and use numbers. But when I put a percentage on my own uncertainty, people get frustrated. One must have a little sympathy for them: humans don’t intuitively “feel” percentage points. So to reiterate that argument: surprise is something you do feel!
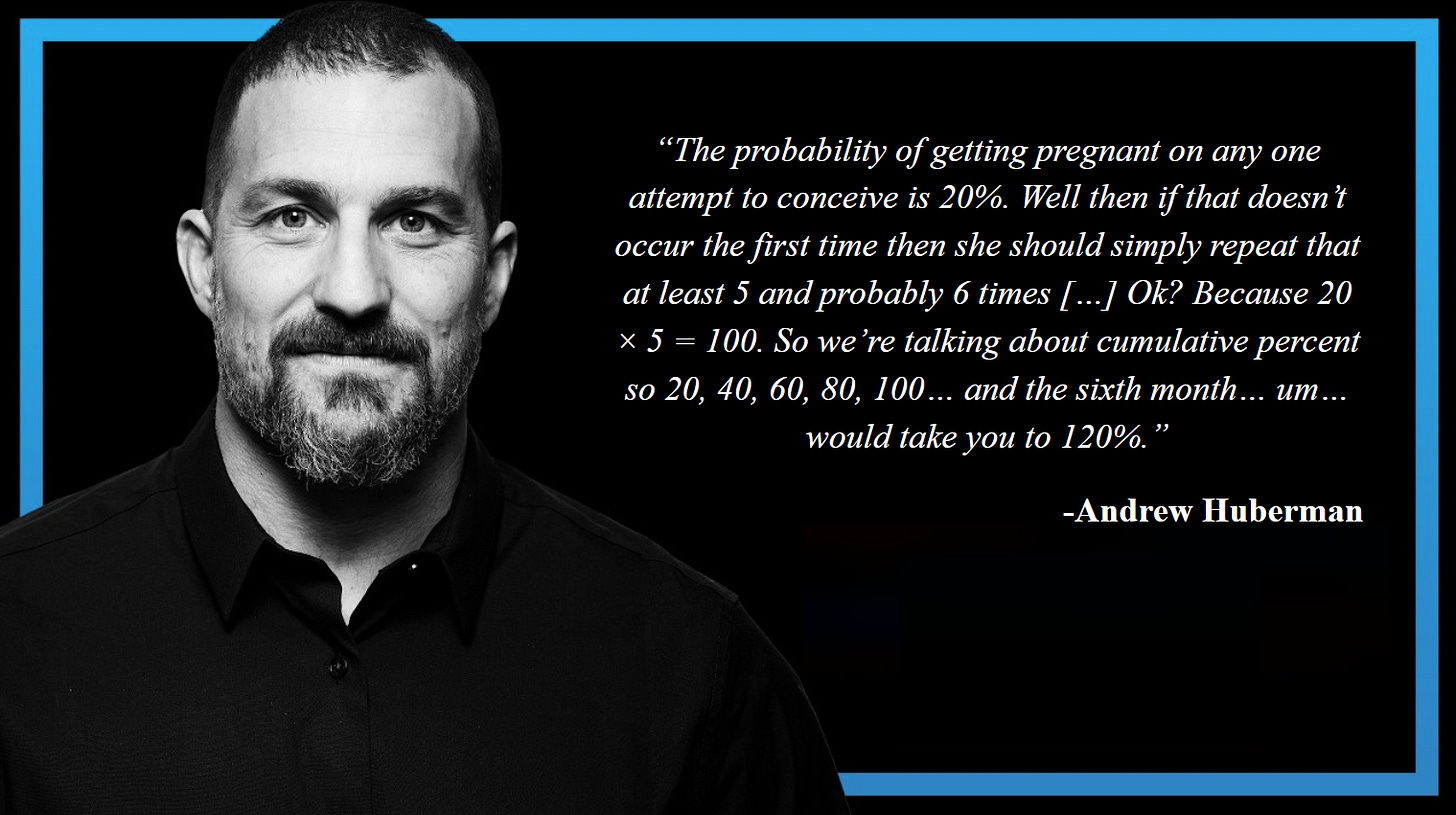
Besides, when they do try to be quantitative…
Don’t hate the thinker, hate the tool for thought
Maybe seeing those makes you despair for humanity so much that you want to avert your gaze from the whole thing. No! Bad attitude! You do not get to give up like that. Even when I tell you that one of them is a Professor of Neuroscience at Stanford 😀
Seriously though - doctors and nurses have to read survival percentage values out all the time. At many points, decisions affecting your life and those of your loved ones have been made based on them. How many lives have been lost to making mistakes like this? You want to make people’s lives better, get them thinking more quantitatively. So: growth mindset for humanity, please. I did not post those quotes so you can complain about them with your enlightened friends. I want you to think of those quotes as telling you what you’re working with if you want to improve things (you want to improve things).
So how do we help those people? We can change their tools for thought. No more probability! Talk about surprise instead!
Maybe: when people see numbers, they want to add them (they expect “linearity”). Then being able to add surprises is a superpower. Let’s give people that superpower by changing education and everyday conversation to use it instead of probability.
Introducing: the Surprice-Dice!
Here’s a funny and helpful thing: it turns out that there is a god-given unit of surprise.
You already know what it means to have a surprise of 0 (“I knew that would happen”) and infinity (“I thought that was impossible”). Well, it turns out there is a thing it means for your level of surprise to be exactly 1.
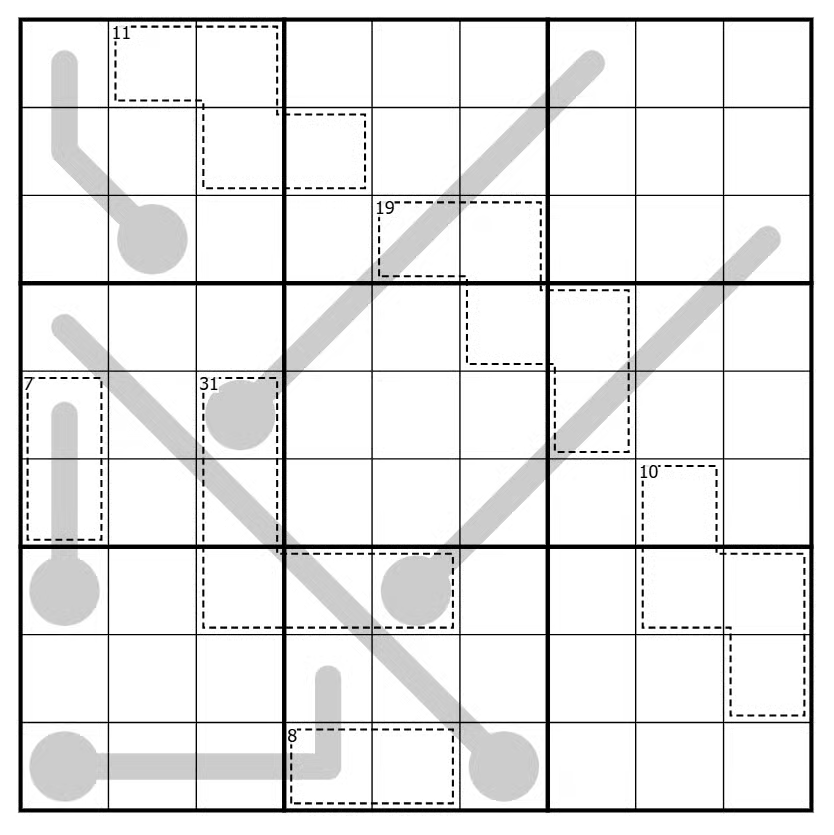
It’s approximately the level of surprise you have when rolling a 30-sided dice and getting 11 or less. To be more exact it’s 1/e, where e is that number people learned about during COVID. 1/e = 0.367… ≈ 11/30.

So, public information campaign: mass-produce 30 sided dice, with numbers 1-11 colored green and 12-30 coloured yellow. Mail one to every household, we’ll double everyone’s IQ overnight! “1 surprise” is one roll of this being 1-11. “2 surprise” is that happening twice. 3 surprise is 3 rolls being 1-11.
How surprised would you be if the democrats lost the next election? More than 2 rolls, or fewer? And that’s how a civilized person talks in 2026!
(yes, I know, “die” not “dice”. But I am a linguistic descriptivist, get used to it!)
To be honest, a revolution in thought of this kind seems improbable would surprise me more than 6 11/30 rolls. Alas, status quo has us locked into probability. Same as electrons having negative charge, pi vs tau, and 3D geometry should be done with the cross product. Still, you might as well give it a go, in your own head or with your kids 🙂
Appendix: sciencey arguments
1. Entropy becomes much more intuitive: it’s “average surprise”, or “expected surprise” (that phrase sounds sounds so ridiculous and I love it). Think about it: with more ordered and predictable (less entropic) things, the average result is less surprising - duh!
2. Bayes theorem gets oh-so-much-nicer too, it’s just adding and subtracting!
2. This has been said for super duper serious science, not just wishy-washy human intuition!
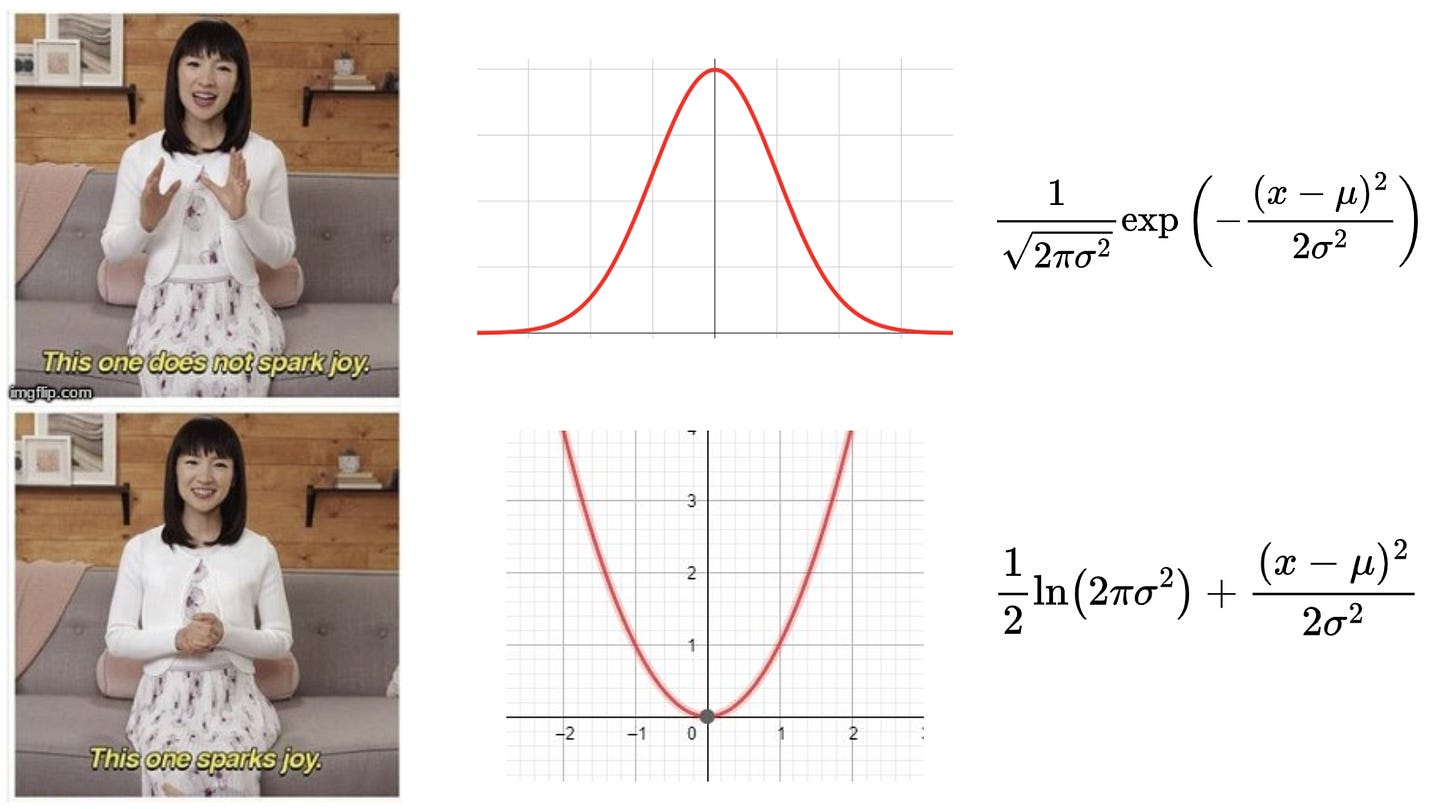
Gaussians are nicer too:
By the way surprise also goes by the name “surprisal” and “log-odds”, but it maps very directly to the intuitive sense of the word so I don’t know why you’d say that!

 The evidence on AI’s effect on those who use it has been coming in, and it’s not good. While it doesn’t effect everyone, it seems to effect most people, and the worst affected, it seems, are the young. Olds have the advantage of growing up in world where they had to learn how to do things themselves. To be sure, phones and social media seem to have had a negative effect on attention span and learning ability, but AI is yet another assault, and it hits the young hardest.
The evidence on AI’s effect on those who use it has been coming in, and it’s not good. While it doesn’t effect everyone, it seems to effect most people, and the worst affected, it seems, are the young. Olds have the advantage of growing up in world where they had to learn how to do things themselves. To be sure, phones and social media seem to have had a negative effect on attention span and learning ability, but AI is yet another assault, and it hits the young hardest.